Hahahahaha
Unintended consequences - what are they going to do once 90% of connections are encrypted, include use of VPNs and encrypted DNS?
This is what they’re promoting.
Host your own encrypted DNS on a VPS in a non-compliant location, use a VPN to connect to it.
So many ways these idiots are cutting their own throats.
Also, let’s list the companies rather than say “Movie Industry”. Or let that be a link to a Wiki article listing all the companies and their holdings.
Fuck em all at this point. I go to maybe 2 movies a year, at most. And I’m cutting subscription services, down to 2 at this point.
As a guy from Russia, I must admit that vpns are not a big problem for censors. They can be easily blocked, including self-hosted ones by protocol detection. And DNS would not do much with IP and clienthello-based blocks. And most users are not enough tech-savvy to constantly switch to new protocols as old ones get blocked.
You have no rights in Russia.
VPNs can’t be categorically banned in the US without major first amendment issues. It’s not a huge technical issue, but unless the courts just throw out the Constitution (a risk that we’re seeing too much of, but still a meaningful bar to cross), there are huge legal barriers to doing so.
Your government doesn’t need to care about legal barriers because you have a dictator who can act unilaterally.
VPNs are not categorically banned in Russia either. Just 95% of them. Categorical ban is not actually required here. Government can just create licensing procedure and license only those VPNs, which follow “rules”. I do not see how this is different from ISP bans.
You realize the tik tok ban bill is also going to ban the use of VPN’s right?
Tor Tor Tor Tor Tor that’s the way the vpn goes.
(In the cadence of the thong song)
Tor is a fed honey pot
While TOR does accept funds from the U.S. federal government it is not a honey pot. Given tor is free and open source it is easy to verify the security of the software.
I use fedora btw (use open source software you fools)
If no one has told you yet. The feds busted a child porn network in the UK that used for because they were hosting over 65% of the exit nodes at the time. If your open source anonymous VPN is hosted by the feds, they can 100% see where the traffic is coming and where it’s going
Please link to a story substantiating this. What I have heard of happening repeatedly is that they trick criminals into communicating outside of tor, running an executable, or just take over the endpoint and nail people eg take over dark web drug markets and use information to track down the folks using it.
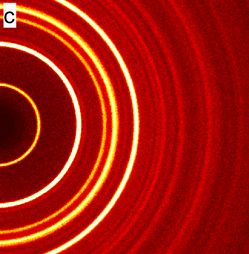
As the article notes, it’s hard to tell just how much of the unmasking comes from exit node control. An exit node will only know what public services are being accessed, without knowledge of any of the user’s addressing/location data (since each node only knows that information about the single hop in each direction). Plus, I’m not even sure exit nodes are used at all when connecting to a tor-hosted service (no need to exit the tor network, after all).
It sounds like the servers are being compromised and then being used to exploit IP-leaking vulnerabilities in how the browser/plugins and Tor network connection are configured.
I’m sure they’ve got a lot of tricks up their sleeves, but exit node control seems like the least significant of them.